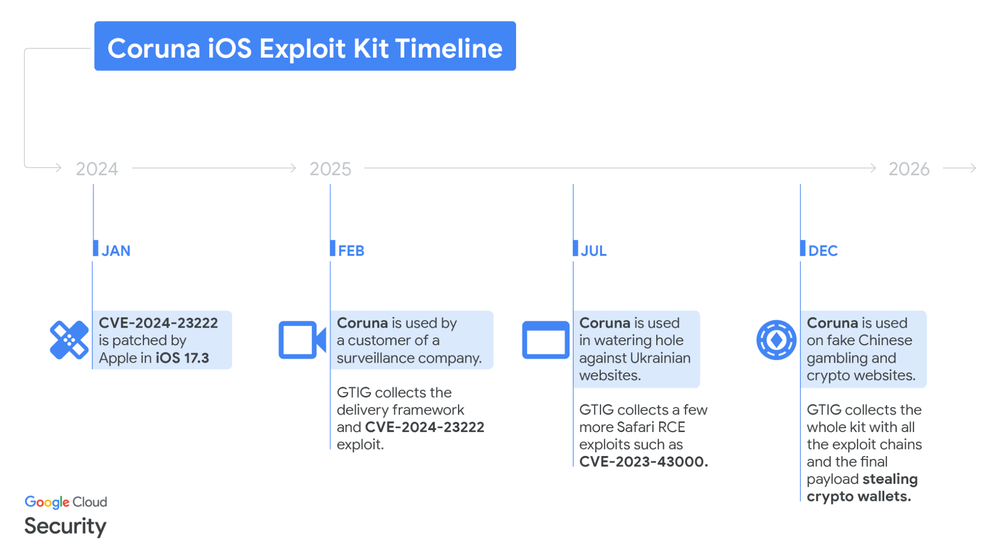
Google's Threat Intelligence Group (GTIG) discovered the "Coruna" exploit kit, targeting iOS devices. This kit comprised 23 exploits, affecting iOS versions 13.0 to 17.2.1, using sophisticated techniques. Initially observed in 2025, the kit was used by a surveillance vendor, then a suspected Russian group, and finally, a financially motivated Chinese group. This proliferation suggests an active market for zero-day exploits. The kit utilizes a JavaScript framework to fingerprint devices and load appropriate exploits including WebKit RCEs. These exploits include CVE-2024-23222, CVE-2022-48503, and CVE-2023-43000. The Coruna kit also contains modules to bypass mitigation features. The final payload is a stager called PlasmaLoader that injects into powerd to steal financial data. The payload targets cryptocurrency wallets, exfiltrating data, and also downloads additional modules. These modules focus on stealing information from various cryptocurrency applications, as indicated by Chinese language log entries. iPhone users are urged to update their devices or enable Lockdown Mode.
cloud.google.com
cloud.google.com