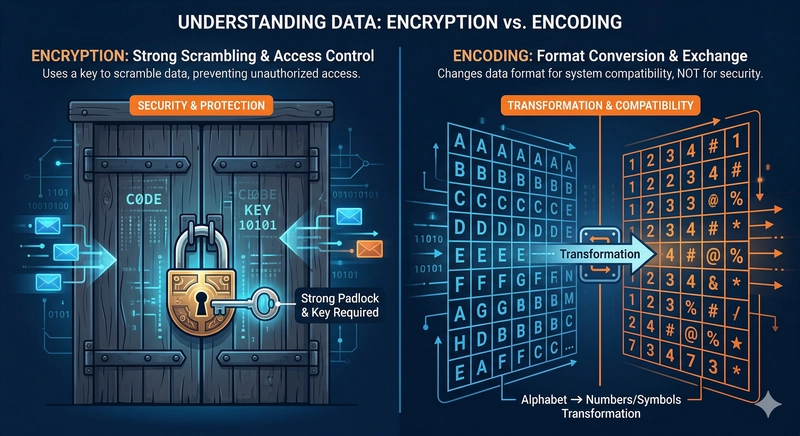
Data breaches are devastating, impacting businesses, trust, and finances, as seen with Sony Pictures, Heartbleed, Code Spaces, and Equifax. These breaches highlight developer responsibility for security, including data flow and storage decisions. Encryption and encoding are distinct; encryption protects with locks and keys, while encoding converts formats. Data security levels range from hardcoded keys to zero-trust models, each with different operational complexity. Security approaches depend on data sensitivity, regulations, threats, and resources. Key compromise is inevitable; systems should anticipate and mitigate damage. Multi-layered defense, including firewalls, authentication, encryption, and key management, is essential. A secure messaging platform requires end-to-end privacy, cost-effective storage, and meticulous key management. Key management uses key vaults like AWS KMS and HashiCorp Vault, KEKs to protect DEKs, and the envelope encryption method.
dev.to
dev.to
Create attached notes ...